Timetable
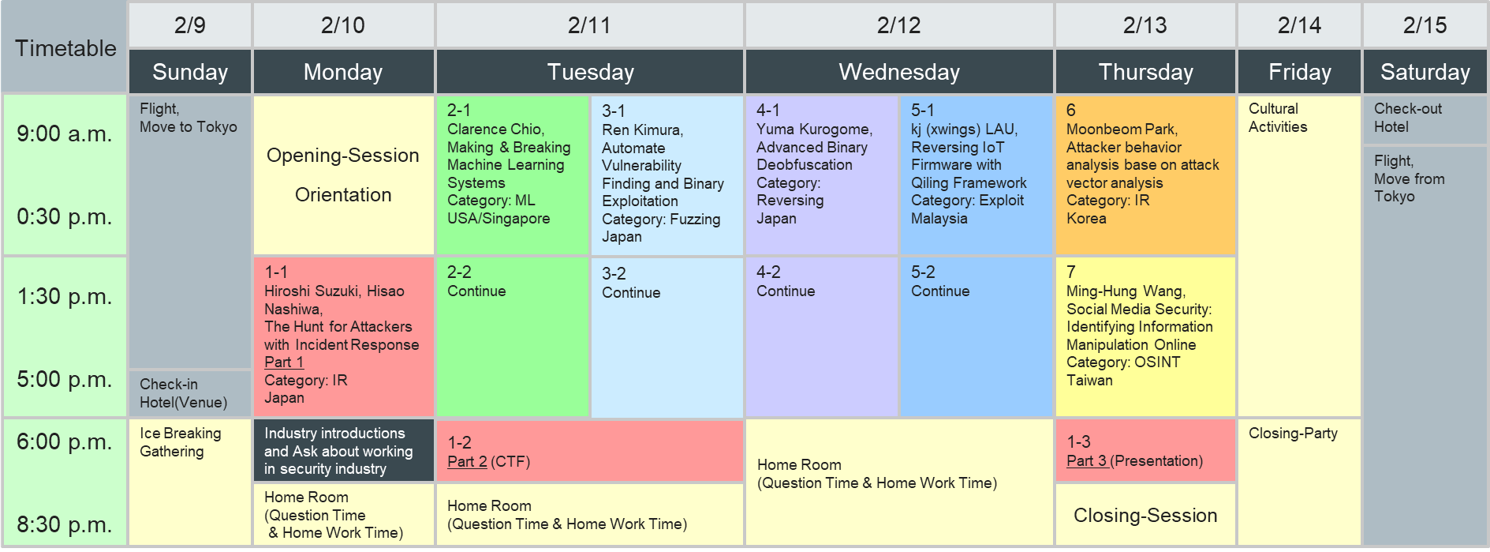
Program
| Title | Making & Breaking Machine Learning Systems |
|---|---|
| Trainer | Clarence Chio - USA/Singapore |
| Abstract | Making & Breaking Machine Learning Systems is a fast paced full day session on machine learning from the Infosec professional’s point of view. In this course, students will not only get hands-on experience with developing adaptive, learning security applications, but also learn the techniques for training, tuning, and evaluating such systems. The course is positioned for hackers who are interested in machine learning, but may not have any practical experience with it. |
| Bio | Clarence Chio is the co-founder and CTO of Unit21, a financial crime fighting company backed by Google's AI venture arm. He is the co-author of the O'Reilly Book "Machine Learning & Security" and teaches two graduate machine learning classes at U.C. Berkeley. Clarence has given talks, workshops, and trainings on machine learning and security at DEF CON, BLACK HAT, RSA, and other security/software engineering conferences/meetups across two dozen countries. He has degrees from the Computer Science department at Stanford University, specializing in data mining and artificial intelligence. |
| Title | Automate Vulnerability Finding and Binary Exploitation |
|---|---|
| Trainer | Ren Kimura - Japan |
| Abstract | In 2016, DARPA hosted the Cyber Grand Challenge (CGC) in order to develop automatic defense systems that can discover vulnerability in real-time. The Challenge was a catalyst for advances in autonomous program analysis, bug finding and much more. Even now 2019, a significant amount of effort is undertaken by people spanning academia, industry and government. |
| Bio | Ren Kimura is a master student in Kobe University. Formerly he was also software security researcher at Carnegie Mellon University CyLab, worked on automating vulnerability finding and exploit generation. He has 5 years of experience and knowledge in system software security and exploit development. |
| Title | The Hunt for Attackers with Incident Response |
|---|---|
| Trainer | Hiroshi Suzuki, Hisao Nashiwa - Japan |
| Abstract | Attendees will perform incident response of a fictional case applied a targeted attack scenario through CTF-style challenges. Students will analyze disk images that will be provided and unravel when and how attackers performed the attack and stole information. Participants will learn comprehensive techniques such as incident response, digital forensics and malware analysis. |
| Bio | Hiroshi Suzuki is a malware analyst, a forensic investigator, an incident responder and a researcher, working for a Japanese ISP company, Internet Initiative Japan Inc. He is a member of IIJ-SECT, which is the private CSIRT of his company. He is especially interested in targeted attacks, their RATs and their attack tools, such as PlugX, Mimikatz and so on. He has over 13 years dedicated to these areas. He has been a speaker and a trainer for international conferences such as Black Hat (USA, Europe, Asia and Japan), FIRST (Annual, TC), GCC (Global Cybersecurity Camp) in Seoul, and trainings for domestic such as Cyber Colosseo for the Tokyo Organizing Committee of the Olympic and Paralympic Games, MWS and Security Camp in Japan. |
| Title | Reversing IoT Firmware with Qiling Framework |
|---|---|
| Trainer | kj (xwings) LAU - Malaysia |
| Abstract | The insecure Internet of Things (IoT) devices and malware attack are growing and they are affecting our day-to-day life. The security industry is struggling to safeguard and cope with such growth and attacks. Abominably, IoT firmware and malware sample analysis remain the two biggiest challanges for the security industry. |
| Bio | KaiJern (xwings), is Lab Director of The ShepherdLab, of JD Security. His research topic mainly on embedded device, hardware security, blockchain security, reverse engineering and various security topics. He presented his findings in different international security conferences like Defcon, HITB, Codegate, QCon, KCon, Brucon, H2HC and etc. He conducted hardware Hacking course in various places around the globe. He is also the owner of hackersbadge.com and actively involved in Unicorn (http://unicorn-engine.org) development. |
| Title | Advanced Binary Deobfuscation |
|---|---|
| Trainer | Yuma Kurogome - Japan |
| Abstract | Reverse engineering is not easy, especially if a binary code is obfuscated. Once obfuscation performed, the binary would not be analyzed accurately with naive techniques alone. In this class, you will learn obfuscation principles (especially used by malware), theory and practice of obfuscated code analysis, and how to write your own tool for deobfuscation. In particular, we delve into data-flow analysis and SAT/SMT-based binary analysis (e.g., symbolic execution) to render obfuscation ineffective. |
| Bio | Yuma Kurogome is a security researcher at NTT Secure Platform Laboratories. His research interest lies in both defensive and offensive perspectives on malware, that is, malware detection/analysis and these evasions. His major research results include talks at industrial venues such as CODEBLUE'15 and Black Hat Europe'19 Arsenal, and an academic paper for ACSAC'19. He is also a former lecturer at the Security Camp, a nation-backed training program for students. |
| Title | Attacker behavior analysis base on attack vector analysis |
|---|---|
| Trainer | Moonbeom Park - Korea |
| Abstract | Analysis hacking technique to analyze the victim system hacked by the attacker, and analysis various logs on the victim system to reconstruct the attacker's behavior. |
| Bio | I'm working in cyber security and incident response sector of South Korea as a general researcher and cyber investigation advisory member of the national investigation agency. Also I'm responsible for research on hacking methods, analyze hacking incident also, profiling the relationships. And I'm not only one of the leaders in Asia's oldest underground hacker group, but also an instructor and mentor in the program(a.k.a BoB) to train ethical hackers in South Korea. |
| Title | Social Media Security: Identifying Information Manipulation Online |
|---|---|
| Trainer | Ming-Hung Wang - Taiwan |
| Abstract | With the rapid development of social networking platforms, a significant amount of user-generated content spreads among the network, and users make online friends who will never meet or gather together in their real life. They comment, organize, and participate from online to offline to express their opinions toward the government. However, many issues also raised from the social media, including information manipulation online. In this course, we will start from data collection, data pre-processing, data manipulation, and then data analysis. We aim to use behaviors to identify potential manipulation online. |
| Bio | I received my Ph.D. in the Department of Electrical Engineering at National Taiwan University in 2017. Before my Ph.D. study, I obtained the M.S. degree in Communication Engineering in 2010 and the B.S. degree in Computer Science in 2008, both from National Tsing Hua University. |
PC spec
| PC spec | - PC spec (hardware, software) |
|---|

